This will be a very short blog post about an old PCAP I did to learn about decrypting WPA2 with Wireshark during my CWNA and CWSP studies. You can read more about it how to decrypt WPA2 here: How to Decrypt 802.11
In 2012 I won the first LG OLED ever made, a curved one with 3D. All the great stuff, it also had a Netflix app that worked great! Many TVs have this, but does all of them use HTTP and not HTTPS? This one used HTTP, and since it did that I wanted to capture some traffic while using this TV to see what is was sending (other than a lot of telemetry data to LG in South Korea, use https://pi-hole.net)
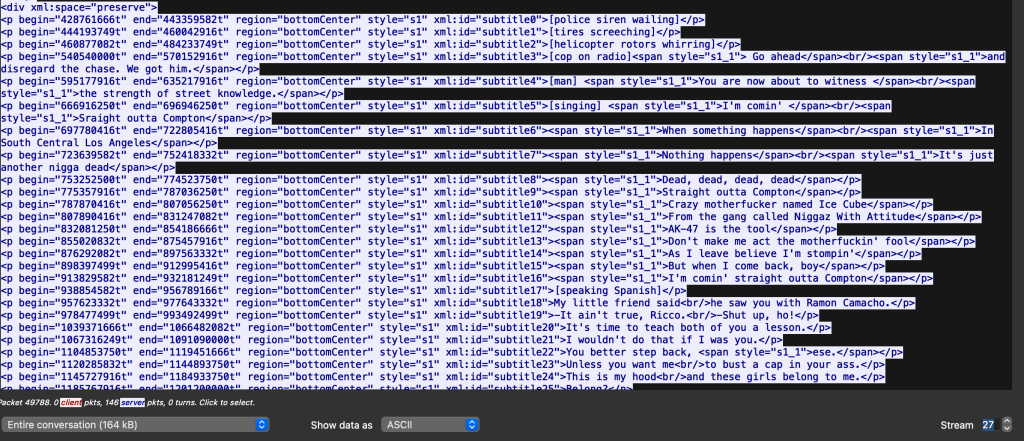
I used a MacBook Air with AirTool and started my capture, I turned on my «Smart» TV and opened up a few apps and started the Ali G movie on Netflix. I made sure I captured a 4-way handshake and saved the pcap and decrypted the traffic.
And there you have it, the entire subtitle of the Ali G movie was received at the second I started the movie, in HTTP. A test later on a newer LG TV is sending this information over HTTPS.
In short, a lot of IoT things with WiFi only and old «Smart» TVs use HTTP and other non-secure protocols. Therefore It can be interesting to see what these devices is sending over the air, and if it is secured. It was pretty fun to see the entire subtitle of every movie I was starting being sent over the air!
Now remember to not decrypt other peoples traffic!
<p begin=»8721212500t» end=»8734142082t» region=»bottomCenter» style=»s1″ xml:id=»subtitle269″>Booyakasha.</p>